Deploy AI Agents
That Act Securely
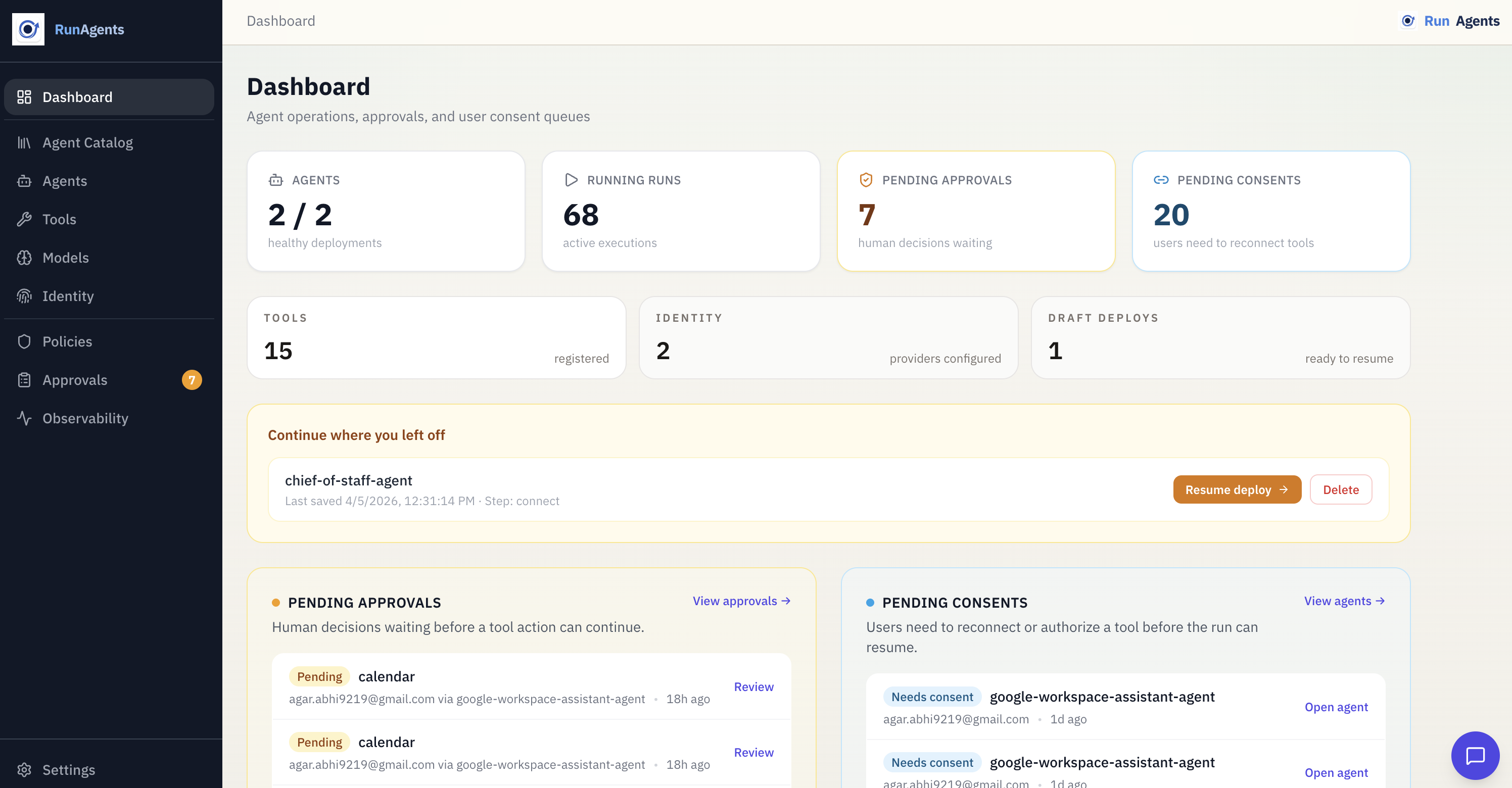
Upload your agent code. Wire it to tools and LLMs. RunAgents enforces identity, access policy, and approval workflows — transparently, with zero code changes.
Use the same governed runtime behind a web app, WhatsApp, Slack, an internal portal, or a custom client.
New in April 2026
CLI v1.2.0, scoped approvals, and stronger operator workflows
RunAgents now ships a much deeper CLI surface for catalog deploys, governance resources, and run debugging, alongside scoped approvals and more reliable pause-and-resume behavior for governed workflows.
-
Scoped approvals
Approve one action, one run, or a short-lived user/agent/tool work window for governed writes.
-
Google Workspace writes
Use policy-controlled Google Calendar event creation alongside delegated-user OAuth and approval workflows.
-
Better pause and resume
Approval and consent workflows resume more cleanly across the console and messaging surfaces such as WhatsApp.
-
CLI v1.2.0
Manage catalog deploys, policies, approval connectors, identity providers, and richer run workflows directly from the terminal.
Platform capabilities
Everything your agent needs to act safely in production
From deploy to approval workflows — the full stack for production-grade AI agents.
-
5-Minute Deploy
Upload Python or TypeScript, auto-detect tools and models, wire, deploy. No Dockerfile, no Kubernetes, no infra.
-
Agent Catalog
Start from maintained production-style blueprints such as the Google Workspace assistant when you want to validate real policy, approval, and OAuth flows.
-
CLI & Natural Language Copilot
runagents copilot— deploy and manage agents by describing what you want. Works in any terminal. -
Any Interface
Put the same agent behind a web app, WhatsApp, Slack, or a custom internal UI. RunAgents handles execution, policy, identity, and approvals behind the surface.
-
Claude Code · Codex · Cursor
Generate a structured action plan with your AI coding tool, validate it, apply it — no console needed.
-
Just-In-Time Approvals
High-risk tool calls pause the agent and notify reviewers via Slack, PagerDuty, Teams, or Jira.
-
Zero-Trust Policy Engine
Every outbound call is authorized. Policies enforce method + path restrictions on every agent identity.
-
Full Run Observability
Structured audit trail per run — user messages, tool calls, approvals — exportable to Splunk, Datadog, ECS.
Architecture
Three-stage secure request flow
Every agent invocation moves through ingress → runtime → egress, with identity and policy enforced at each stage.
-
Stage 1 · Ingress
JWT validated at the edge. User identity extracted and forwarded as
X-End-User-IDheader through the entire call chain. -
Stage 2 · Runtime
Agent executes — LLM calls route through the gateway, tool calls route through the policy engine. Logs structured events per turn.
-
Stage 3 · Egress
Every outbound call intercepted: identity verified, policy evaluated, OAuth token injected. Approval workflows triggered on deny.
Read the full architecture guide
Core concepts
Security is the default, not an add-on
The user who triggered the agent is identified at ingress. That identity travels — unchanged — to every tool the agent calls.
- JWT validated and unpacked at the platform edge
X-End-User-IDheader forwarded automatically to all downstream tools- External APIs see the real end-user, not a shared service account
- Full traceability: every tool call is linked to a real human identity
Agents can only call tools they have been explicitly granted access to. Policies enforce not just which tools, but which operations.
- Policies define URL/tag rules with
allow,deny, orapproval_required - Capability checks enforce method + path level (
POST /chargesvsGET /customers) - Default posture is deny unless a bound policy explicitly allows access
- Approval workflows are triggered by policy rules, not by legacy tool flags
High-risk operations pause the agent. An admin reviews the exact payload, approves or rejects, and the platform auto-resumes.
- Payload hash verification — the approved request must match exactly what the agent sends
- Notification via Slack (with OIDC identity linking), PagerDuty, Teams, or Jira
- Time-limited grants — access expires after a configurable TTL
- Full resume automation — no manual re-triggering after approval
Get started in seconds
One command to deploy from the terminal
# Install
curl -fsSL https://runagents-releases.s3.amazonaws.com/cli/install.sh | sh
# Configure
runagents config set endpoint https://your-workspace.try.runagents.io
runagents config set api-key YOUR_API_KEY
# Deploy with natural language
runagents copilot
> deploy this folder as billing-agent
Analyzing source files...
✓ Detected: stripe tool, gpt-4o-mini model
✓ Tool registered: stripe
✓ Agent deployed: billing-agent (Running)
Ready to deploy your first agent?
Free trial. No credit card. Running in 5 minutes.